Sometimes we want to change any parameter of our current user interface quickly, let’s say terminal length or idle timeout, but we don’t know which user interface we are currently using. To check that we use display user-interface command. Then we try to find the “+” mark in the command output, which means that this is our current user interface. After that we have to go back to our user interface configuration and change its parameters. Why not to do that in a quicker manner?
[labnario]display user-interface
Idx Type Tx/Rx Modem Privi ActualPrivi Auth Int
0 CON 0 9600 - 15 - P -
33 AUX 0 9600 - 0 - P -
+ 34 VTY 0 - 0 3 A -
35 VTY 1 - 0 - A -
36 VTY 2 - 0 - A -
37 VTY 3 - 0 - A -
38 VTY 4 - 0 - A -
50 VTY 16 - 15 - A -
51 VTY 17 - 15 - A -
52 VTY 18 - 15 - A -
53 VTY 19 - 15 - A -
54 VTY 20 - 15 - A -
UI(s) not in async mode -or- with no hardware support:
1-32
+ : Current UI is active.
F : Current UI is active and work in async mode.
Idx : Absolute index of UIs.
Type : Type and relative index of UIs.
Privi: The privilege of UIs.
ActualPrivi: The actual privilege of user-interface.
Auth : The authentication mode of UIs.
A: Authenticate use AAA.
N: Current UI need not authentication.
P: Authenticate use current UI's password.
Int : The physical location of UIs.
In case we want to change any parameter of our current user terminal interface, without checking which user interface we are using, “current” option for the user-interface command can be used.
Let’s look at VTY configuration:
Read More »
BGP MED attribute on Huawei router
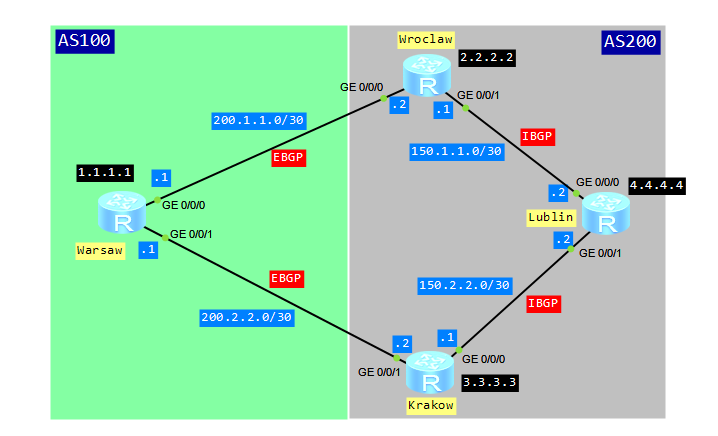
Some time ago I published article about BGP local preference attribute. Today I’d like to show you how to configure BGP MED attribute.
What is it for?
The multi-exit discriminator MED determines an optimal route for incoming traffic of an AS. When a BGP device obtains multiple routes to the same destination but with different next hops from EBGP peers, the BGP device selects the route with the smallest MED value as the optimal route. Simply saying, configuring MED attribute, we would like to show the next hop for traffic coming from EBGP peer. The MED attribute is exchanged only between two neighboring ASs. The AS that receives the MED attribute does not advertise it to any other ASs.
Let’s look at typical scenario for MED attribute configuration:
assigning multiple IP addresses to network interface
Why might we want to assign multiple IP addresses to the same interface? The following are the most common scenarios:
- hosts in the network segment use IP addresses on different networks
- there are not enough host addresses on a logical network segment, suppose a /24 address space and 300 hosts
How to configure multiple IP addresses on Huawei devices?
Let’s configure a pair of routers connected via a Gigabit Ethernet link and use four different logical networks.
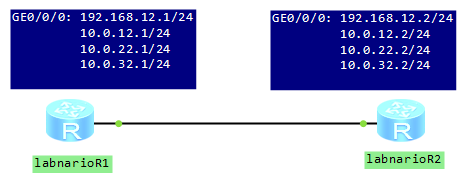
[labnarioR1]int gi 0/0/0 [labnarioR1-GigabitEthernet0/0/0]ip add 192.168.12.1 255.255.255.0 [labnarioR1-GigabitEthernet0/0/0]ip add 10.0.12.1 255.255.255.0 sub [labnarioR1-GigabitEthernet0/0/0]ip add 10.0.22.1 255.255.255.0 sub [labnarioR1-GigabitEthernet0/0/0]ip add 10.0.32.1 255.255.255.0 sub
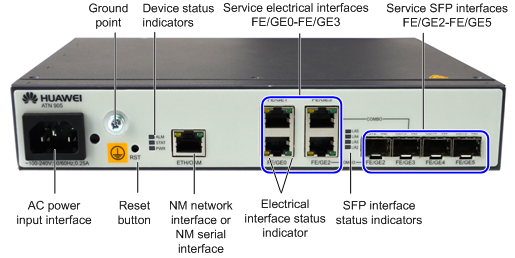
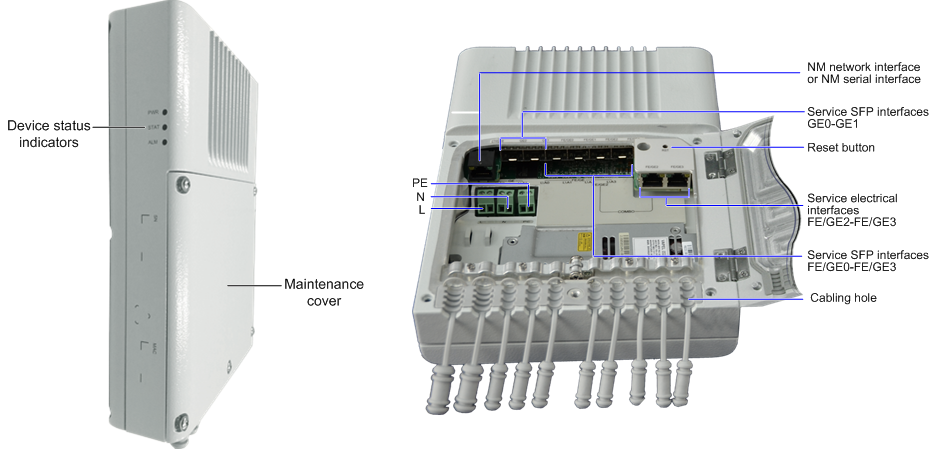
indoor and outdoor Huawei ATN905
As you know I try to avoid products descriptions here, on this blog. But last time I had possibility to see ATN905 boxes, available in the indoor and outdoor types. You can install them in various environment. The application scenarios of ATN905 are divided into the small-cell base station bearer scenario and the Ethernet demarcation device (EDD) scenario.
Let’s look at the pictures of the two types of this router:
from Huawei CLI – check …
Very useful command, especially when you are preparing and executing upgrade of a software of Huawei carrier class devices, like NE40E and CX600. Let’s look what can be checked by this command:
<labnario>check ? hardware-compatibility hardware compatibility startup Check the version of the resource file system-software system-software version check version
I personally use “check hardware-compatibility” before all planned upgrades. During a preparation phase of an upgrade, you have to read software release notes, to be sure that all software and hardware components will be compatible with the new software. You can check hardware compatibility by the command, instead of searching software documents.
Imagine that you’ve just uploaded a new software to CFcard of a router. The new software is v600r006c00spc300.
<labnario>check hardware-compatibility v600r006c00spc300.cc Slot# BoardType Result Detail - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - 3 CR57LAXFB00 Compatible NA 4 CR57LAXFB00 Compatible NA 5 CR57EMGFB20 Compatible NA 6 CR57EMGFB20 Compatible NA 9 CR57SRU200A5 Compatible NA 10 CR57SRU200A5 Compatible NA 11 CR57SFU200C0 Compatible NA 12 FRA200A Compatible NA 13 FRA200A Compatible NA
It’s very simple, isn’t it?
 Labnario Huawei From Scratch
Labnario Huawei From Scratch